Cyber insurers are tightening requirements, raising premiums, and demanding proof that organizations can prevent credential misuse and contain lateral movement. In 2025, Privileged Access Management (PAM) has become one of the most decisive factors in whether a business can secure … Read More
RDP
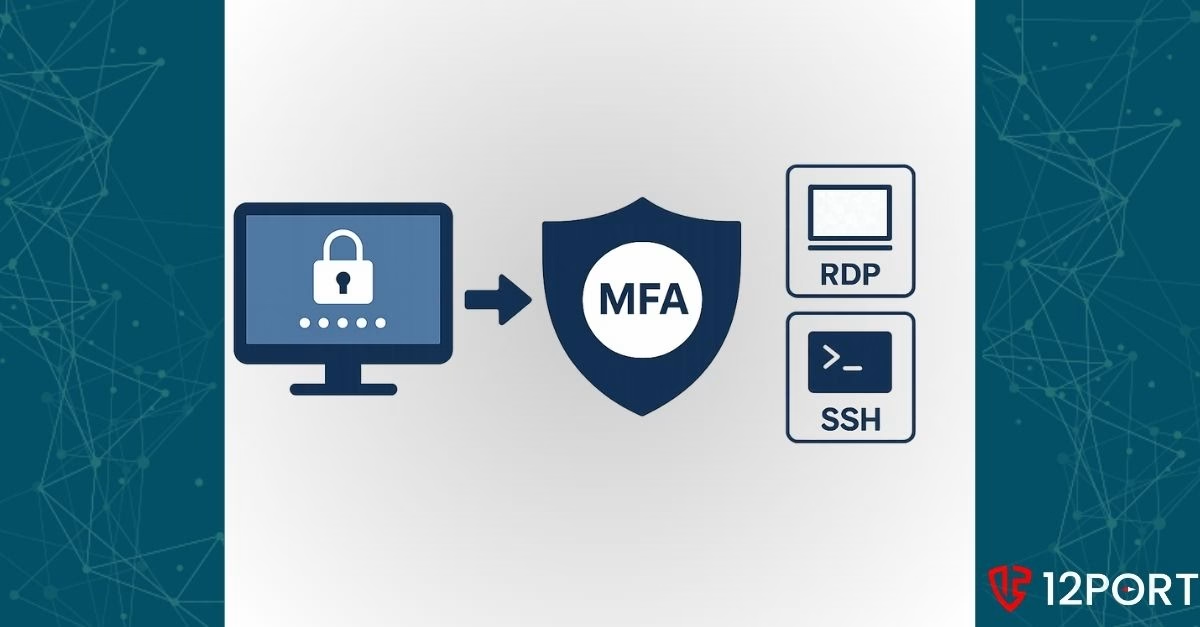
How to Enable MFA Before RDP and SSH Sessions
Remote access is essential for modern enterprises. IT administrators, DevOps teams, and vendors need to connect to critical infrastructure using Remote Desktop Protocol (RDP) or Secure Shell (SSH). But many organizations still allow these sessions without enforcing a critical security … Read More

How to Segment SSH and RDP for Zero Trust Success
RDP and SSH remain top targets for attackers because they offer direct access to the systems that matter most. As covered in our earlier post (Why You Should Segment RDP & SSH), segmenting these high-risk protocols is one of the … Read More

Why You Should Segment RDP & SSH
Securing remote access pathways often feels like an endless battle against evolving threats. Attackers continually search for exposed protocols, especially those that provide direct or near-direct access to critical systems. Remote Desktop Protocol (RDP) and Secure Shell (SSH) stand out … Read More

